Hello team,
We noticed this behavior from patch policy wherein patches are not being included in the patch policy action. And when we investigated further, it seems that the patch policy cannot include superseded fixlets in the patch policy actions because no machines are relevant for the fixlet once it is superseded.
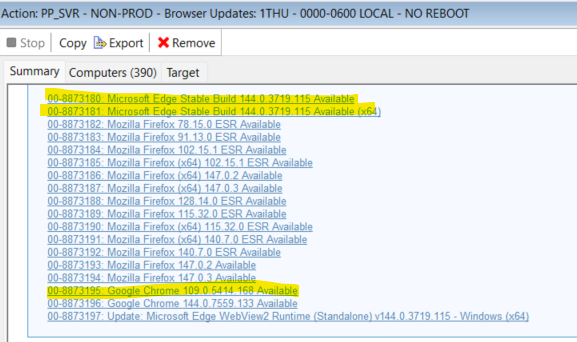
In our environment, patch policies for browsers are set to run on non-prod servers first (FEB12-17) while the patch policy for prod servers are only during sunday ( Feb22, Mar01, Mar08). Our patch policies (one for non-prod and one for prod) are set to refresh only once which for this month, Feb11 because we want our non-prod and prod servers to have the same version level.
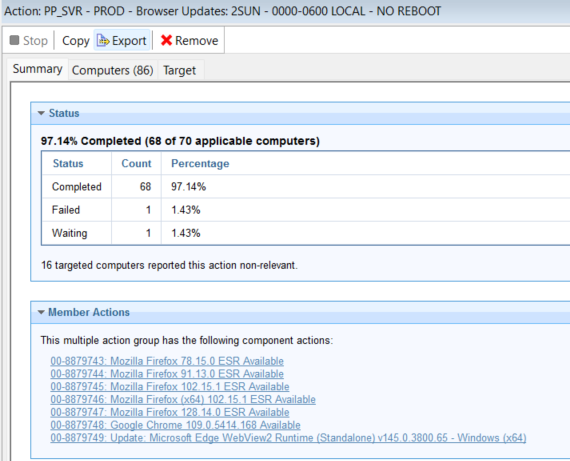
All the patch policy action from FEB12-17 contained the same components from the browser. However, when we were investigating the issue, the first patch policy for prod scheduled last Feb22 did not include the same MS Edge fixlet. We checked the WebUI patch policy external fixlets and the MS edge was there but was not included on the patch policy action. Upon checking, same goes with google chrome latest version.
When we checked the latest release google chrome released a newer version last Feb18 while MS edge released their newer version last Feb17. I was thinking that due to the original filxet being superseded, servers returned as not relevant for the fixlet and since no servers are relevant for it, patch poilicy action did not include it.
Can you confirm if this is the expected behavior for superseded fixlet in the patch policy action? If yes, wouldn’t it make more sense that the fixlet inside the patch policy would still be relevant for the servers because of environments that aim to have their servers be on the same version level? And if this is indeed the expected behavior, I guess the workaround is to have the patch policy schedule create the action WHILE they are still relevant for the fixlet
Thanks for any input.