OpenSSL version (Starting from 3.0.0 to below 3.0.7) are affected by CVE-2022-3786 and CVE-2022-3602. Described on OpenSSL Security Advisory website:
“A buffer overrun can be triggered in X.509 certificate verification, specifically in name constraint checking. Note that this occurs after certificate chain signature verification and requires either a
CA to have signed the malicious certificate or for the application to continue certificate verification despite failure to construct a path to a trusted issuer. An attacker can craft a malicious email address to overflow four attacker-controlled bytes on the stack. This buffer
overflow could result in a crash (causing a denial of service) or potentially remote code execution.”
“A buffer overrun can be triggered in X.509 certificate verification, specifically in name constraint checking. Note that this occurs after certificate chain signature verification and requires either a CA to have signed a malicious certificate or for an application to continue certificate verification despite failure to construct a path to a trusted issuer. An attacker can craft a malicious email address in a certificate to overflow an arbitrary number of bytes containing the `.’ character
(decimal 46) on the stack. This buffer overflow could result in a crash(causing a denial of service).”
https://www.openssl.org/news/secadv/20221101.txt
BigFix Inventory helps you to discover if the affected OpenSSL version are deployed on your environment.
• To discover all versions of OpenSSL, you can use the discovery provided by the template signature in the official BFI catalog.
• In case you would like to understand which systems are affected by the OpenSSL installation, we have created a custom signature which detects versions of OpenSSL affected by the CVE (mentioned in the beginning of the article): https://bigfix.me/signature/details/1261
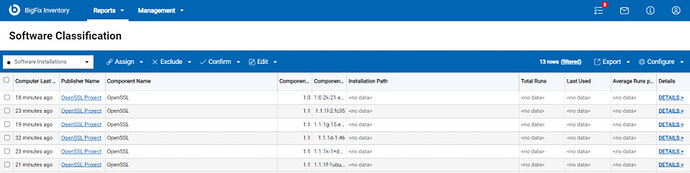
1. BigFix Inventory report of on OpenSSL packages using existing template signature
For generic audit, you can use an already existing template signature that searches on BigFix endpoints for OpenSSL packages.
2. BigFix Inventory search for only affected OpenSSL versions
For a detailed auditing of CVE affected OpenSSL installations, BigFix Inventory provides an additional custom signature that searches for OpenSSL RPM package files with the pattern openssl-3* and collects information about all occurrences of affected versions. The regular component version displayed after discovery is 0.any_version and the detailed version contains information about the current patch level.
Please find below step for using the custom signature:
- Download the signature file from URL provided under every type of discovery described.
- Login to BigFix Inventory.
- Go to Management → Catalog Customization.
- Import the file with the custom signature.
- Run an import process.
- Make sure that the catalog was propagated to the endpoints (automatically created action for propagation the endpoint executed on all applicable endpoints).
- Run a software scan on the endpoints.
- Ensure the Upload Software Scan Result fixlet is running.
- Run an import process to import the scan results.
- Verify the results on the reports.
Please note that results of scan are limited direct installation of OpenSSL packages, in case they are embedded into some third-party tool, they won’t be detected.
Raghavendra,
BigFix Inventory Team