Confluence Server and Data Center for versions 1.3.0 – 7.18.1 are affected by vulnerability CVE-2022-26134. BigFix Inventory helps you discover if your software for version 7.x is still affected or already patched. In this article, you will learn how to use custom signatures to detect this.
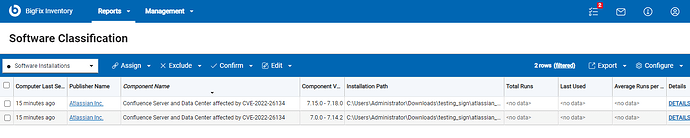
Definition of two components were published on BigFix.me to detect affected Confluence Server or Data Center:
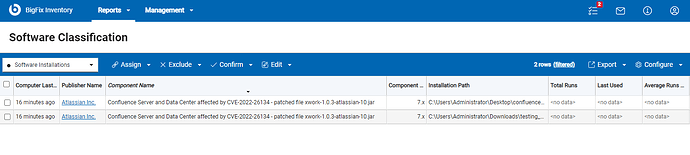
and one component to detect if such software is already patched:
-
“Confluence Server and Data Center affected by CVE-2022-26134” for versions 7.0.0 - 7.14.2 gives us information if such software is affected by .jar files mentioned CVE. The signature of this component verifies if exists at least one of vulnerable jar files:
xwork-1.0.3.6.jarorwebwork-2.1.5-atlassian-3.jarin particular path:<confluence-install>/confluence/WEB-INF/lib/
The signature is available at: https://bigfix.me/signature/details/1250 -
“Confluence Server and Data Center affected by CVE-2022-26134” for versions 7.15.0 - 7.18.0 gives us information if such software is affected by .jar file mentioned CVE. Signature of this component verifies if exists vulnerable .jar file:
xwork-1.0.3-atlassian-8.jarin particular path:<confluence-install>/confluence/WEB-INF/lib/
The signature is available at: https://bigfix.me/signature/details/1251 -
For all 7.x versions component “Confluence Server and Data Center affected by CVE-2022-26134 – patched file xwork-1.0.3-atlassian-10.jar” was created to check if software is already patched. The signature checks if the
xwork-1.0.3-atlassian-10.jarfile has been uploaded and if the vulnerable .jar files (mentioned in previous points) have been removed.
The signature is available at: https://bigfix.me/signature/details/1252
Procedure for patching CVE on affected Confluence Server and Data Center is available on the official Confluence Support webpage: Confluence Security Advisory 2022-06-02 | Confluence Data Center 8.8 | Atlassian Documentation
Process how to import custom signatures is presented below:
- Download the signature file from URL provided under every type of discovery described.
- Login to BigFix Inventory.
- Go to Management → Catalog Customization.
- Import the file with the custom signature.
- Run an import process.
- Make sure that the catalog was propagated to the endpoints (automatically created action for propagation the endpoint executed on all applicable endpoints).
- Run a software scan on the endpoints.
- Ensure the Upload Software Scan Result fixlet is running.
- Run an import process to import the scan results.
- Verify the results on the reports.