ok it’s been about 12± hours since I reverted back to the original reporting times of the analysis and it doesn’t seem that much different.
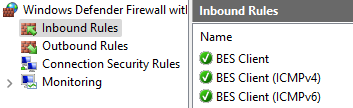
During my fall down the rabbit hole yesterday, I noticed that there’s a column called Client Evaluation - Last UDP Ping. I have a good number of machines that are not receiving that ping. They reside in vlans where other machines do get the ping so it’s not a corporate fw issue. We do use the Windows Firewall, and I got curious on and was able to get on some machines in which the BESClient fw inbound rules were missing! How does that even happen? How can the client be installed but somehow missing the fw rules? The end users are not admins to the machines so it’s not the end user just deleting rules.
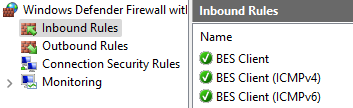
I exported the fw rules from my machine and took out the 3 registry lines and came up with this relevance and action to add them to the registry and to restart the client afterwards.
not exists key “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\FirewallRules” of native registry
regset64 “[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\FirewallRules]” “{{E9671E3F-116D-4260-ACB3-362EEE9D3BB5}}”=“v2.30|Action=Allow|Active=TRUE|Dir=In|Protocol=58|App=C:\Program Files (x86)\BigFix Enterprise\BES Client\BESClient.exe|Name=BES Client (ICMPv6)|”
regset64 “[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\FirewallRules]” “{{68913DCF-3D98-4DFC-87BD-C0F56DD9FF2B}}”=“v2.30|Action=Allow|Active=TRUE|Dir=In|Protocol=1|App=C:\Program Files (x86)\BigFix Enterprise\BES Client\BESClient.exe|Name=BES Client (ICMPv4)|”
regset64 “[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\FirewallRules]” “{{F52B19FB-7CA6-4354-8EFD-E2DB8B23CDB5}}”=“v2.30|Action=Allow|Active=TRUE|Dir=In|App=C:\Program Files (x86)\BigFix Enterprise\BES Client\BESClient.exe|Name=BES Client|”
// Delay for 10 seconds
waithidden timeout /t 10
// Restart BESClient service
wait cmd /C net stop “BESClient” & net start “BESClient”
funny thing is that I searched the forum and I found someone who mentions fixlet 518 Windows Firewall is Blocking BES Traffic but it doesn’t come up as relevant. I looked over the relevance and with my limited knowledge I don’t know if it picks up missing BES Client fw inbound rules.
so back to my registry fixlet - I tested this on a few test machines and it worked. I then ran it on the machines in question but still they’re showing up not receiving the UDP ping in the analysis.
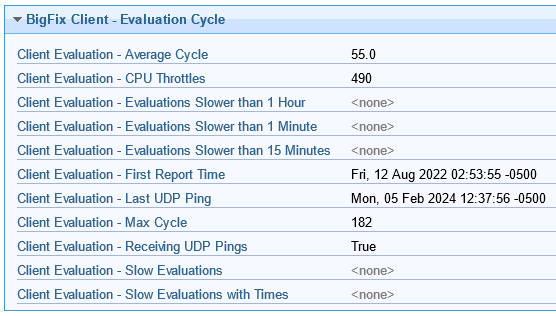
I can only assume this could be related to what we’re experiencing with the clients not reporting on a timely fashion and taking long to eval?
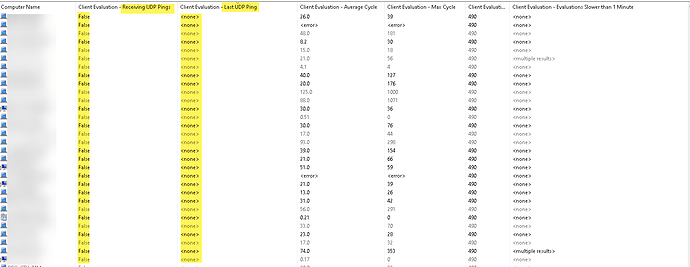
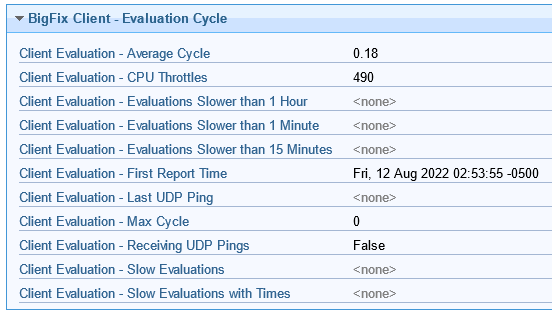
Here’s the analysis sorted by Client Evaluation - Receiving UPD Ping:
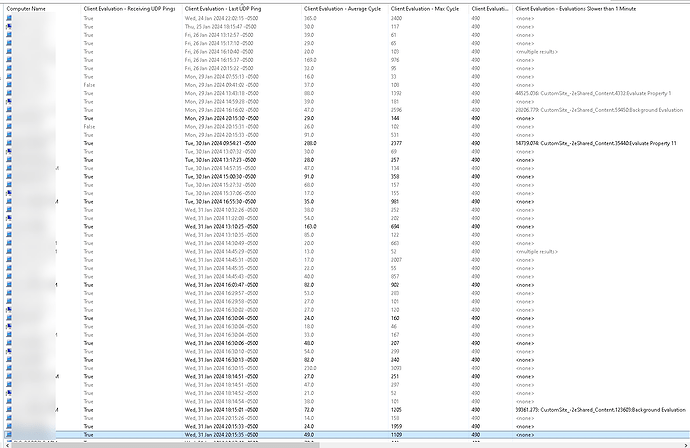
If I sort it by Last UDP Ping then I have all recent days, many for today and yesterday to about a week back.